Most organizations don’t suffer breaches because they ignore security. They suffer them because something small slips through unnoticed.
- An account with more access than it needs.
- A system that behaves one way in testing and another in production.
- A control that works well on its own, but not once everything is connected.
So what are penetration testing services, and why do so many businesses rely on them? At their core, they are a way to challenge assumptions. They deliberately test whether everyday gaps like these could be exploited in the real world, before someone with malicious intent decides to find out for themselves.
How penetration testing is different from vulnerability scanning

Both vulnerability scanning and penetration testing play a role in keeping systems secure, but they’re designed to answer very different questions.
A vulnerability scan highlights known issues. Missing patches. Outdated software. Common configuration gaps. This type of security testing is useful for maintaining day‑to‑day hygiene and visibility.
Penetration testing asks something more practical: if this issue exists, what could someone actually do with it? By safely attempting exploitation, penetration testing shows which weaknesses lead to real access, real data exposure, or real operational impact.
Vulnerability Scanning vs Penetration Testing
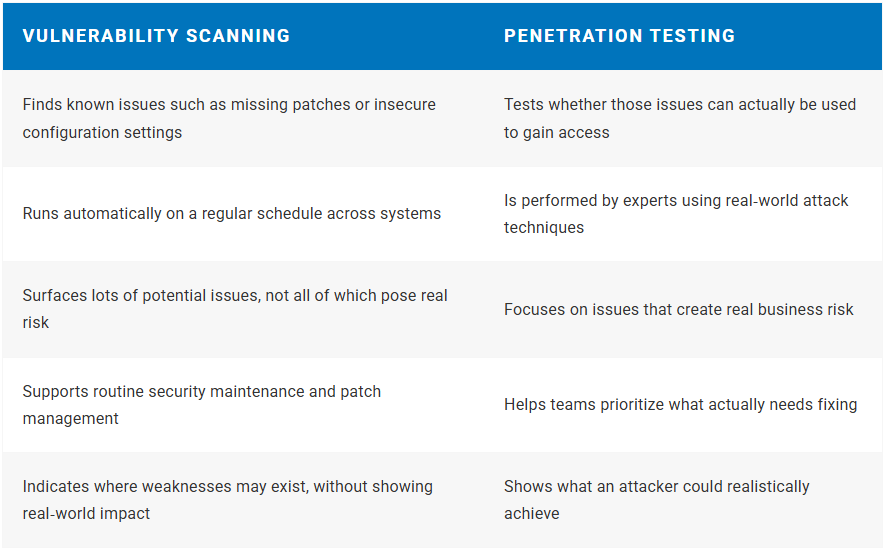
| Vulnerability scanning | Penetration testing |
|---|---|
| Finds known issues such as missing patches or insecure configuration settings | Tests whether those issues can actually be used to gain access |
| Runs automatically on a regular schedule across systems | Is performed by experts using real‑world attack techniques |
| Surfaces lots of potential issues, not all of which pose real risk | Focuses on issues that create real business risk |
| Supports routine security maintenance and patch management | Helps teams prioritize what actually needs fixing |
| Indicates where weaknesses may exist, without showing real‑world impact | Shows what an attacker could realistically achieve |
Common types of penetration testing
Penetration testing is rarely one‑size‑fits‑all. Most organizations focus on testing the areas where risk, data, or regulatory exposure is highest. In practice, that usually means a combination of the following.
Network security testing
Network security testing looks at how systems connect and trust each other, both from the outside and internally. It helps uncover paths an attacker could follow once any initial access is gained. In healthcare environments, this often centers on networks connected to electronic medical record systems. Testing here helps validate whether those systems are properly segmented and protected, which is essential for patient safety and meeting requirements such as HIPAA.
Application security testing
Application security testing focuses on how web and business applications handle logins, permissions, and sensitive data. This is where subtle logic issues often surface, particularly in custom or rapidly updated applications. For legal and accounting firms, this type of testing is especially relevant. Applications routinely store confidential client information, and data privacy obligations such as CPRA mean access controls need to work exactly as intended, not just in theory.
Cloud and infrastructure testing
Cloud and infrastructure testing examines identity management, configurations, and shared responsibility in cloud environments. These areas are common sources of risk and are not always picked up by automated tools. For publicly traded companies, this type of testing often supports confidence around SOC 2 controls by validating that access, logging, and segregation of duties hold up under realistic conditions.
Internal penetration testing
Internal penetration testing simulates what could happen if a user account or device is compromised. It focuses less on how someone gets in and more on what happens next. This approach is particularly valuable for companies operating under frameworks such as ISO 27001, PCI DSS, GDPR, or HIPAA. It helps answer a practical question leaders often ask: once someone is inside, are the right limits actually in place?
The penetration testing process
Before a penetration test starts, there’s a simple conversation between the business and the testing team. The aim is to agree what will be tested and what won’t, so the exercise stays useful, safe, and focused on what actually matters.
One key part of that conversation is how much information the testers start with. This shapes how the test feels and what kinds of questions it’s designed to answer.
Black‑box testing
Network security testing looks at how systems connect and trust each other, both from the outside and internally. It helps uncover paths an attacker could follow once any initial access is gained. In healthcare environments, this often centers on networks connected to electronic medical record systems. Testing here helps validate whether those systems are properly segmented and protected, which is essential for patient safety and meeting requirements such as HIPAA.
What penetration testing does not do
It doesn’t try to uncover every possible issue inside the environment. It focuses on realistic entry points, not total coverage.
White‑box testing
In a white‑box test, the business shares detailed information upfront. This might include architecture diagrams, configurations, or even access to code. This allows the test to go deeper more quickly and is often used when the goal is to validate how well controls are working, rather than to simulate surprise.
What penetration testing does not do
It doesn’t assume attackers already have this level of access. It’s about depth of assurance, not likelihood.
Grey‑box testing
Grey‑box testing sits between the two. Testers are given a small amount of information, but not the full picture. This reflects common real‑world scenarios, such as a compromised user account or limited third‑party access, and often strikes a good balance between realism and efficiency.
What penetration testing does not do
It doesn’t predict exactly how a breach would start. It helps understand what could happen once limited access exists.
Clarity Where It Matters Most

Penetration testing is one of the fastest ways to move from “we think we’re secure” to “we know where the gaps are.” At iwx, it’s not treated as a one‑off exercise. It’s part of a practical, long‑term security approach focused on visibility, prioritization, and helping teams make better decisions over time.